We know that iPhones (later than A14 chip) are pretty much secure in BFU. Now the question is, does Lockdown Mode completely remove the AFU attack vector or was this phone actually BFU. Either way it sounds like lockdown mode is very useful.![]()
![]()
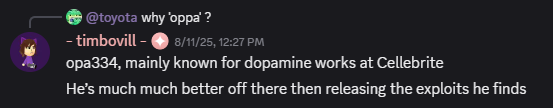
“New court record from the FBI details the state of the devices seized from Washington Post reporter Hannah Natanson”
This is high profile espionage case related to leak of TOPSECRET documents, therefore probably all possible tech was used to gain access to the devices.
Page 5:
In the upstairs of the house, investigators located a powered-off silver MacBook Pro with a black case, an Apple iPhone 13*, a Handy branded audio recording device, and a Seagate portable hard drive. See id. ¶ 26. Investigators seized these devices. The iPhone was found powered on and charging, and its display noted that the phone was in “Lockdown” mode*
Page 6:
The Computer Analysis Response Team (CART) began processing each device to preserve the information therein. The Handy recorder and the Seagate portable drive have been processed, but no review has occurred. See id. ¶ 37. Because the iPhone was in Lockdown mode, CART could not extract that device*. See id. ¶ 35. Similarly, the personal MacBook Pro could not be imaged yet. See id. ¶ 36. The Garmin watch was not processed before this Cout’s Standstill Order, and no further processing will occur until further order of the Court. See id. ¶ 37*