Hi all,
I am posting here because I’m sure many of you are running your own self-hosted services!
I am just beginning my homelabbing journey, trying to regain ownership over my stuff and cutting down on subscription services that I can self-host. I have done quite a bit of research, but most articles/tutorials assume either 1. a lot of previous knowledge and don’t explain many details, or 2. that you’re just starting out and they don’t explain many details.
Anyways, here is what I am trying to do and the setup I have currently:
I want the ability to self-host a NAS, repurposing some HDDs I rescued from old PCs, and I want to be able to host my own photos, music and TV shows. I currently have an old laptop running Debian and have setup a local network share using Samba.
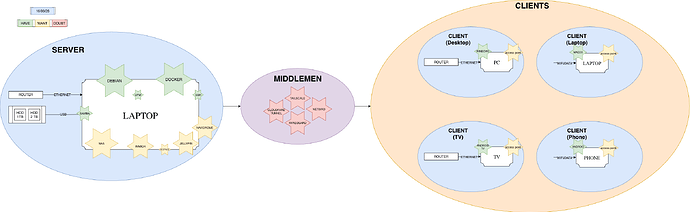
Here’s a visual graph of my setup, with everything I have installed and everything I want:
In green I have the services I have installed, in yellow those that I want to set up, and in red those that I am having trouble figuring out.
Here is my main dilemma: I want to be able to access my files/music/images from anywhere remotely without having to send that data through third party servers. I want total privacy.
I also want a setup that is completely secure and robust, meaning no outside-attackers could get my data and my local network is absolutely and under all circumstances safe.
As far as I have been able to read and understand, people concerned with the secure part of things usually set up Tailscale. However, reading their Privacy Policy, they certainly are not as respecting as I would like. Moreover, only being able to sign up using a Third Party Login is a definite no-go for me.
Wireguard seems to have a similar issue, especially when dealing with IP Adressesses.
Other options I have, admittedly, not looked into as much as I should, seem to be NetBird, Cloudfare Tunnels, NGINX Reverse Proxies…
All of this to say:
What is a 100% privacy respecting, 100% secure way to remotely access my home server? What are your setups looking like these days?
I should say, I do not care how complicated/convoluted the setup would have to be. My goal with this project is to truly learn how to master these tools, and I have enough time to do some research and truly understand how everything works.
I am sure I’m missing many steps and I’m sure I have many misconceptions, so please feel free to correct me and enlighten me with anything I may be doing wrong. I have only been doing this for a couple months, so everything and anything is welcome!
Thanks a lot in advance!