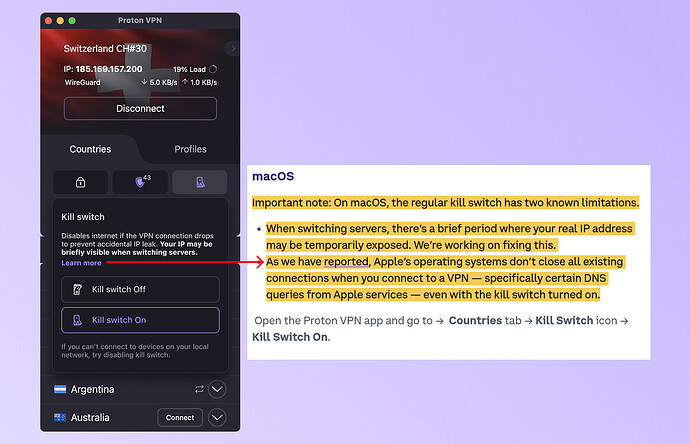
Fair pushback, let us be more direct than our last response was. The current implementation of the macOS kill switch does not reliably protect IP during server switches.
There was an in-app alert, but it required context to interpret correctly, and our KB articles weren’t explicit enough about this limitation.
We’ve updated both:
-
The KB article has been revised and is live here.
-
We’re updating the in-app kill switch modal to state the risk plainly, which will be rolled out with the next update: "Disables internet if the VPN connection drops to prevent accidental IP leak. Your IP may be briefly visible when switching servers.
The deeper fix is already in progress. We’ve been rebuilding our network stack with a native WireGuard implementation, developed in-house, that includes a native kill switch maintaining the tunnel through server switches. Like we mentioned previously, the timeline for the fix is within the first half of our Spring/Summer roadmap cycle.
On why this wasn’t surfaced more clearly to users sooner: we don’t have a satisfying answer. Our user base has historically skewed toward Windows and mobile, and Mac had not received the same level of documentation scrutiny. To be clear, we are not trying to justify this, however it’s important to provide context for why the gap existed and went unaddressed longer than it should have.
We’re reviewing how security-relevant limitations get flagged in both our KB process and in-product copy going forward.